Definition: Authorization is the basis by which the authority to complete the various stages of a transaction is delegated. This is often a restriction by organization code, budget number, or other organizational or financial entity defined restriction.
What is the importance and functions of the authentication Authorisation and accounting?
AAA stands for authentication, authorization, and accounting. AAA is a framework for intelligently controlling access to computer resources, enforcing policies, auditing usage, and providing the information necessary to bill for services.
What is the difference between authentication authorization and accounting?
Techopedia Explains Authentication Authorization and Accounting (AAA) Authentication refers to unique identifying information from each system user, generally in the form of a username and password. Accounting refers to the record-keeping and tracking of user activities on a computer network.
Which feature of network Security records what the user does including what is accessed the amount of time the resource is accessed and any changes that were made?
AAA accounting feature
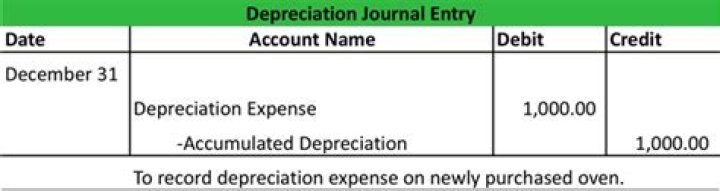
The AAA accounting feature allows the services that users are accessing and the amount of network resources that users are consuming to be tracked.
What is the difference between AAA authentication and authorization?
A. Authentication verifies a username and password, and authorization handles the communication between the authentication agent and the user database. Authentication identifies and verifies a user who is attempting to access a system, and authorization controls the tasks the user can perform.
What are the three A’s of security?
authentication, authorization, and accounting
Then, we’ll dive into the three As of information security: authentication, authorization, and accounting.
What is the primary difference between AAA authentication and authorization?
What is the primary difference between AAA authentication and authorization? A. Authentication identifies and verifies a user who is attempting to access a system, and authorization controls the tasks the user can perform.
Why is authentication needed?
Authentication is important because it enables organizations to keep their networks secure by permitting only authenticated users (or processes) to access its protected resources, which may include computer systems, networks, databases, websites and other network-based applications or services.
What are the types of authentication?
What are the types of authentication?
- Single-Factor/Primary Authentication.
- Two-Factor Authentication (2FA)
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Password Authentication Protocol (PAP)
- Challenge Handshake Authentication Protocol (CHAP)
- Extensible Authentication Protocol (EAP)
Which of the following is the most secure form of authentication?
Nowadays, the usage of biometric devices such as hand scanners and retinal scanners is becoming more common in the business environment. It is the most secure method of authentication.
What happens first authorization or authentication?
Authentication is done before the authorization process, whereas authorization process is done after the authentication process. 1. In authentication process, the identity of users are checked for providing the access to the system. It is done before the authorization process.
What are the 5 factors of authentication?
Five Authentication Factor Categories and How They Work
- Knowledge Factors. Knowledge factors require the user to provide some data or information before they can access a secured system.
- Possession Factors.
- Inherence Factors.
- Location Factors.
- Behavior Factors.
What is a difference between Radius and Tacacs +?
RADIUS was designed to authenticate and log remote network users, while TACACS+ is most commonly used for administrator access to network devices like routers and switches.
What is the strongest authentication method?
What is Beyond Identity? Beyond Identity combines two of the strongest authenticators: biometrics and asymmetric keys. It eliminates the password and provides an extremely secure authentication since the user’s identity is only stored locally on the device and it cannot be moved.